News, Breakthroughs & Recognition
Belfort pushes the boundaries of encrypted computation. This page shares our latest milestones, recognition, customer stories, and insights.
Live insights & milestones
Stay up to date with our latest announcements, product developments, industry recognition, and expert insights in secure, large-scale encrypted computation.
San Francisco / Leuven, March 25, 2026 — Belfort, a company pioneering the infrastructure layer for Encrypted Compute, today announced that Google has become its first paying customer. The engagement marks a key milestone in advancing Encrypted Compute from research into practical systems.
The announcement comes amid a massive global buildout of AI infrastructure, with industry leaders projecting over $1 trillion in compute demand in the coming years. As AI systems move into real-world deployment, a new challenge is emerging: how to run these systems on sensitive data without exposing it. Recent pressure tests of enterprise AI systems, including a widely reported case involving an internal platform at McKinsey & Company [link], has shown how quickly autonomous agents can gain access to sensitive data once it is processed in plaintext.
Encrypted Compute offers a solution by enabling the processing of sensitive information without decryption, preserving cloud flexibility while eliminating exposure risks. While the concept has existed for years, performance limitations have prevented widespread adoption. Belfort addresses this bottleneck through a high-performance acceleration layer purpose-built for encrypted workloads.
Advancing Encrypted Compute
Beyond performance, usability is the other primary obstacle, specifically the difficulty of converting calculations to FHE friendly operations. To address this, Google is developing HEIR (heir.dev), a compiler and development platform that simplifies the integration of these techniques into practical systems. Combined with Belfort’s high-performance acceleration layer, this creates a unified stack for Encrypted Compute, from developer tooling to execution.
“Google’s ability to connect advanced research with large-scale systems makes them an ideal partner for Belfort. It enables us to evaluate and improve our technology against real-world workloads, helping ensure we are building a robust and scalable foundation for Encrypted Compute.”
— Laurens De Poorter, Belfort Co-Founder & CEO
At its core, Encrypted Compute is powered by Fully Homomorphic Encryption (FHE), widely regarded as the holy grail of cryptography, which enables arbitrary computations to be performed directly on encrypted data. Belfort’s platform is designed to make FHE practical by delivering the performance and usability required for real-world applications.
“Bringing Fully Homomorphic Encryption into the mainstream requires a robust ecosystem of interoperable tools and high-performance hardware. Belfort’s commitment to building a transparent, compiler-friendly acceleration layer is exactly the kind of industry-standard approach needed to move FHE from theoretical research into production environments. We believe that this synergy between advanced hardware acceleration and user-centric software abstraction will be the cornerstone of future secure computation infrastructure, enabling a new class of enterprise applications that prioritize data sovereignty.”
— Jeremy Kun, Google HEIR Lead
About Belfort
At Belfort, we believe that in an AI-first world, trust is all you need and the future of computing is encrypted. Belfort enables that vision by accelerating Encrypted Compute to make it practical at scale, ensuring that sensitive data can be processed without ever being decrypted. A spin-off from KU Leuven’s world-renowned COSIC lab, Belfort combines breakthroughs in hardware and algorithms to build the next layer of secure computing. The company has offices in San Francisco, USA, and Leuven, Belgium. https://belfortlabs.com/
About HEIR
HEIR (heir.dev) is a compiler toolchain for fully homomorphic encryption (FHE) designed for developers and researchers to build production-grade, privacy-preserving applications. Maintained by Google's FHE/HEIR team within Safeworks, it supports application developers, compiler engineers, and hardware designers in advancing secure, encrypted systems for Alphabet and society at large. https://heir.dev/
Belfort kicks off commercialisation push with Google deal
Belfort announces Google as its first paying customer, marking a key step toward practical encrypted compute.
The Challenge: Screening Without Decrypting
Swift transactions are encrypted in transit. That is by design. But fraud screening and sanctions checks need to happen in real time, as payments flow. Today, that means decrypting the transaction to run the check, then re-encrypting it. The data is exposed, even if only briefly, and the pipeline has to be trusted end to end.
The goal Swift set with us was simple to state and hard to achieve: screen encrypted transactions against sanctions lists in real time, without ever decrypting them. Fully Homomorphic Encryption makes this mathematically possible. The problem has always been that FHE is far too slow to meet real-time requirements. A check that takes 4 minutes per transaction is not fraud detection, it is a batch audit.
At Belfort, we are changing that. In this post, we explain how we brought encrypted fuzzy name matching’s latency down from 4 minutes to below 1 second and what that means for real-time fraud screening at scale.
Why Fuzzy Matching?
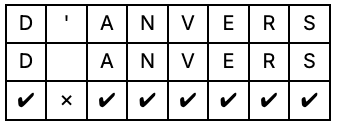
Sanctions screening and fraud detection depend on matching names in transaction data against watchlists. This is harder than it sounds: names are misspelled, transliterated differently across languages, or contain minor variations. "D'Anvers" and "DAnvers" typically refer to the same person but a strict character-by-character comparison will fail.
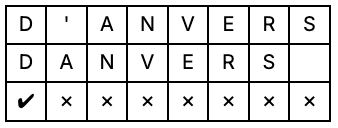
More specifically, we need to compute the edit distance or Levenshtein distance, which counts the minimum number of insertions, deletions, or substitutions needed to transform one string into another.
The catch is that Levenshtein distance is computationally expensive. The cost scales quadratically with the string length. Under FHE, where every operation carries significant overhead, this was completely impractical until recently.
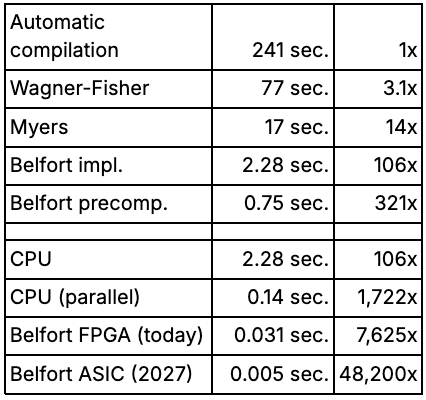
Algorithmic Optimisations: 321x Faster in Software
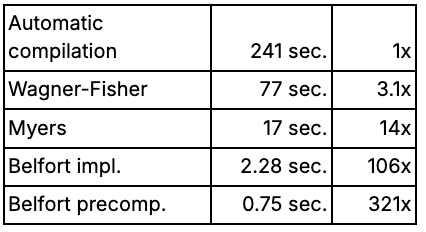
Together with Swift, we defined a concrete target: run Levenshtein-based name matching on fully encrypted bank transactions, without ever decrypting the data. The starting point, an automatically compiled FHE implementation of the standard Wagner-Fisher algorithm, took 241 seconds per transaction. That is a research curiosity, not a product.
The first lever is algorithm choice. Not all algorithms are equal under FHE, and the standard Wagner-Fisher approach turns out to be a poor fit. The Myers algorithm, which uses a boolean representation instead of full integers, maps far more naturally to FHE's native operations. This results in a runtime of17 seconds: 14x faster, no hardware changes.
Three further FHE-specific optimisations — a more compact data representation, computing two results from one expensive operation, and collapsing a multi-step calculation into a single lookup — bring this to 2.28 seconds and a 106x total speedup.
The final software gain came from an unexpected observation: at this point, most of the remaining compute resource was spent comparing character pairs, not computing the edit distance itself. Since the sanctions list is not encrypted, those comparisons can be precomputed once and reused. That single insight delivers another 3x improvement, reaching 0.75 seconds and 321x over the original baseline.
Hardware Acceleration: Closing the Gap to Real Time
The AI boom was fueled by GPUs, and similarly, FHE will benefit from dedicated hardware units. The first such units are only now becoming available, and their speed is expected to increase significantly in the coming years.
For a fair comparison, it is worth noting that TFHE operations can be parallelised across cores. Exploiting this on a 32-core machine reduces average processing time to 0.14 seconds, a 16.3x speedup over a non-parallelised implementation. For longer strings, speedups of up to 30x were observed, approaching the theoretical maximum of 32x. This is the realistic CPU baseline against which dedicated hardware should be measured.
On that baseline, Belfort's FPGA accelerator makes a dramatic difference. Running on dedicated hardware explicitly designed for TFHE, the same workload completes in 0.031 seconds — a 7,625x speedup over the original baseline, and more than 4x faster than the parallelised CPU. This is the level of performance that makes real-time encrypted screening a realistic proposition.
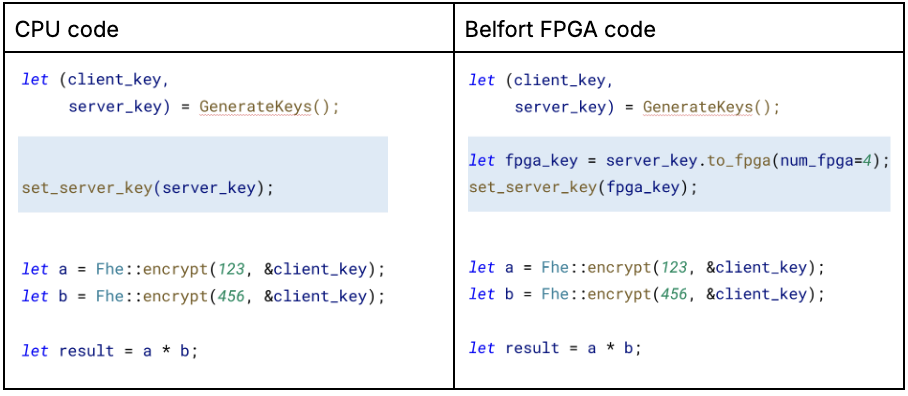
Our Belfort accelerator integrates seamlessly with the TFHE-rs library. To run your program, you'll need a Belfort-enabled computer (Belfort's latest-gen Velox accelerator is publicly available for early access) and to modify three lines in your TFHE-rs code's preamble. Below is an example of these changes.
What This Means for Financial Institutions
At sub-second latency, encrypted fuzzy matching becomes operationally viable for the first time. Transactions can be screened against sanctions lists without ever being decrypted, eliminating the exposure window that today's systems all share. No need to trust the cloud provider, the hardware, or the administrator. Trust the mathematics.
This matters beyond Swift. Any institution that needs to screen sensitive data against a reference list, whether correspondent banks, payment processors, or compliance teams operating across jurisdictions, faces the same tradeoff. Belfort's approach resolves it.
"Fraud screening and data privacy have always been in tension at Swift. To check a transaction against a sanctions list, you need to read it, which means exposing it. Working with Belfort, we saw for the first time a credible path to resolving that tradeoff: running fuzzy matching directly on encrypted transactions, without ever decrypting them. That changes the conversation."
- Nam-Luc Tran, Product Owner Anomaly Detection, Swift
What's Next
Now is the right time to start building with FHE. The performance barriers that made it impractical are coming down faster than most people expect. Our FPGA accelerator is available today on Amazon AWS. The ASIC roadmap targets 5ms latency by 2029, opening the door to real-time encrypted screening at full transaction throughput.
If you are working on sensitive data workflows in financial services, compliance, or fraud detection, we would like to hear from you.
Further Reading
This work builds on research from KU Leuven’s COSIC research group on efficient encrypted string matching. In particular, see “Leuvenshtein: Efficient FHE-based Edit Distance Computation with Single Bootstrap per Cell” presented at the USENIX Security Symposium 2025, which introduces a new algorithm for computing Levenshtein distance under Fully Homomorphic Encryption with far fewer bootstrapping operations.
Link: https://www.usenix.org/conference/usenixsecurity25/presentation/legiest
About Belfort
At Belfort, we believe that in an AI-first world, trust is all you need and the future of computing is encrypted. Belfort enables that vision by accelerating encrypted compute to make it practical at scale, ensuring that sensitive data can be processed without ever being decrypted. A spin-off from KU Leuven’s world-renowned COSIC lab, Belfort combines breakthroughs in hardware and algorithms to build the next layer of secure computing. The company has offices in San Francisco, USA, and Leuven, Belgium. https://belfortlabs.com.
[Swift] Encrypted fraud detection
For Swift, Belfort cut encrypted sanctions screening from 4 minutes to <1 second using FHE optimizations and hardware acceleration, enabling real-time checks without decrypting transactions.
San Francisco / Leuven – March 5, 2026 – Belfort today announced Velox, the latest iteration of its encrypted compute accelerator. Velox runs on the AMD Alveo V80 FPGAs and achieves more than 3x performance improvement over its previous generation. Velox is the fastest known acceleration for TFHE workloads and will be available both in the cloud and on-premises.
Founded as a spin-off from KU Leuven, Belfort enables computation on encrypted data, helping organizations unlock the value of sensitive data without compromising privacy.
Encrypted Compute
As AI systems become more powerful and increasingly integrated into sensitive workflows, protecting the underlying data becomes critical. Sensitive information such as patient records, financial transactions, and proprietary business intelligence must remain secure.
Traditional approaches require decrypting data before processing, exposing sensitive information to infrastructure and system operators.
Encrypted compute changes that. By enabling AI inference and computation on fully encrypted inputs, organizations can process sensitive data while ensuring it is never exposed, even to the infrastructure running the model. The result is AI that is not only powerful, but provably private.
Introducing Velox
For nearly a decade, the team has focused on bringing encrypted compute from research into production systems. Velox represents a major step forward.
The platform upgrades Belfort’s previous FPT system running on AMD Alveo U55C FPGAs to the next-generation Alveo V80, unlocking significant performance gains.
“We implemented several hardware and mathematical optimizations in our accelerator, resulting in a lean architecture that is both flexible and highly performant. The initial release of Velox runs at 300 MHz, with further clock improvements planned in future iterations.”
Furkan Turan, Belfort Co-Founder & Head of Engineering
Velox also launches with native multi-FPGA support, transparently partitioning and distributing encrypted workloads across all available accelerators, with zero user-side orchestration. This capability is not currently available on other encrypted compute platforms.
Throughput (PBS/s) Benchmarks:
Designed for real-world use
Alongside hardware improvements, Belfort has significantly expanded its software integration layer.
Velox integrates with widely used fully homomorphic encryption frameworks, including Google HEIR and TFHE-rs, allowing developers to run encrypted workloads using familiar tooling.
“Our goal is to make encrypted compute accessible. Customers can request access and be running workloads on our hardware within minutes. A dual-Velox system can sustain over 260 confidential ERC-20 token transfers per second, demonstrating the performance required for real-world applications.”
Michiel Van Beirendonck, Belfort Co-Founder & CTO
What this enables
Encrypted compute allows organizations to process sensitive data without ever exposing it, enabling entirely new privacy-preserving applications.
2x faster encrypted fraud detection:
In collaboration with SWIFT, Belfort developed a fraud detection workflow that checks encrypted bank transactions against sanction lists. With Velox, a single check takes 7.63 seconds on one FPGA, roughly 2x faster than previous implementations, bringing encrypted fraud detection closer to practical deployment.
20x faster confidential stablecoin payments:
Velox enables confidential blockchain transactions to be validated while the transaction details remain encrypted. This makes it possible to process stablecoin payments on public infrastructure without revealing transaction amounts or counterparties, a major unlock for business transactions.
8.5x faster AES transciphering:
Velox also delivers 8.5x faster conversion of data protected with standard encryption, such as AES, into fully homomorphic encryption, making it practical to process sensitive data in the cloud while it remains encrypted. In practice, this means organizations can deploy this technology without changing existing client-side encryption.
Together, these advances make it increasingly feasible to use sensitive data without ever revealing it, unlocking new possibilities across finance and other data-sensitive industries.
(Early) Access
Velox will be available both in the cloud and as an on-premise deployment.
Organizations interested in testing encrypted compute workloads can request early access to the Velox platform.
About Belfort
At Belfort, we believe that in an AI-first world, trust is all you need and the future of computing is encrypted. Belfort enables that vision by accelerating encrypted compute to make it practical at scale, ensuring that sensitive data can be processed without ever being decrypted. A spin-off from KU Leuven’s world-renowned COSIC lab, Belfort combines breakthroughs in hardware and algorithms to build the next layer of secure computing. The company has offices in San Francisco, USA, and Leuven, Belgium. https://belfortlabs.com.
Belfort launches Velox, the world’s fastest TFHE Accelerator
We're launching a major upgrade of our accelerator platform to bring Encrypted Compute closer to real-world deployment.